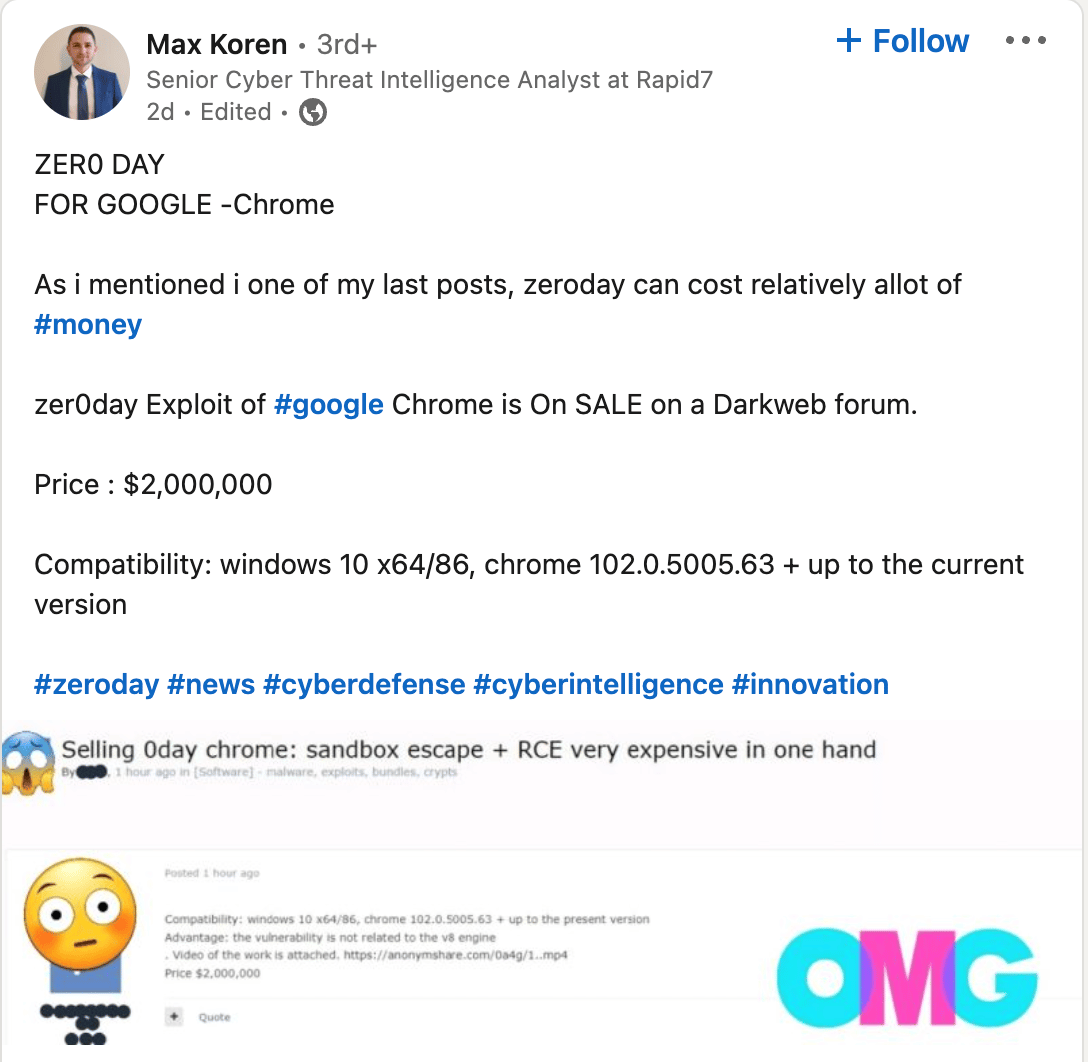
According to a recent LinkedIn post from a Senior Cyber Threat Intelligence Analyst at Rapid7, there is a new Google Chrome zero-day vulnerability that is under active exploitation in the wild! Google hasn’t discovered or patched this vulnerability, and someone is selling the exploit for $2m on the dark web! A market for zero days has existed for a long time but only recently has the process become more commercialized with the rapid increase of zero days and the emergence of brokers like Zerodium, who offer to pay for these exploits and sell them on to clients in the private and public sectors.
What does this mean for my company?
Well, do you use Google Chrome? If so, the exploit code being auctioned off may lead to your organization being victimized through various forms of cybercrime.
When this vulnerability eventually becomes known, developers will try to patch it to stop the attack. However, keep in mind that it can sometimes take a long time before the vulnerability is identified. And even once this zero-day is patched and the patch released, most companies will not be quick enough to implement the patch.
Zero-days can be more dangerous than other forms of attack because the vulnerabilities are known ONLY to the attackers. So, if they breach your network, they can attack immediately, or sit and wait for when the time is right.
How do I prevent a zero-day attack?
This is where it gets interesting. A Threatpost article from a few years ago posed the question – “how do you defend against a vulnerability you don’t know about?” This is the perplexing nature of zero-day exploits.
When you leave your house, you make sure the windows and doors are locked. A zero-day attack is like a home invader who finds a master key to the locks on your house that you never knew existed and can gain entry anytime they want. It is not until your jewelry and TVs are missing that you realize there is a problem. Even worse, this master key can also grant the intruder access to any house using the same locks.
The industry standard is to wait until a patch is released and then patch the vulnerabilities. But how can you patch an unknown vulnerability?
The answer is Seraphic!
This is where Seraphic is revolutionizing cyber security, starting with the browser. Seraphic stops attacks that take advantage of weaknesses in the browser (unknown yet, 0-day vulnerabilities, or known, n-day vulnerabilities).
Our approach to exploit prevention is different – it is not based on any detection technique – Seraphic creates unpredictability by adding an abstraction layer on top of the JavaScript Engine (JSE) that prevents the exploitation of the JSE. This reduces the need to patch your browsers after every new vulnerability patch is published.
So again, Seraphic does not try to detect but assumes that all code received by the browser from any source even from the most trusted domain is malicious. Our patent-pending “Chaos Engine” makes the JSE environment unpredictable and thus unexploitable while valid code is executed normally.
So, if you recall the “home invasion” analogy when that burglar finds that master key and attempts to get into your house, Seraphic blocks the use of any master key, when entering your house and introduces a new type of lock that continuously changes with every attempt of a burglar to pick it. Malicious code tries to open org locks, but with Seraphic, we change the lock every time.