What is Data Leakage / Data Loss and How Can it Be Prevented?
Data leakage and data loss are the unauthorized transfer or exposure of corporate information. It can be the result of accidental negligence or deliberate theft by employees or third parties.
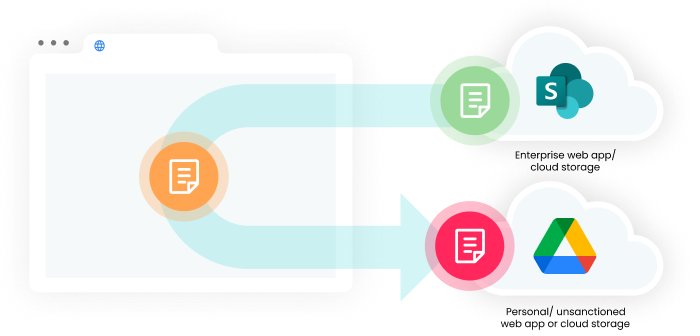
Data Leakage on browsers and desktops
Browsers and desktop SaaS apps have joined—if not replaced—email and removable storage as the top enterprise data loss vectors. The proliferation of sensitive data across apps and cloud storage exposes organizations to increased risk of:
- Data leakage from accidental or negligent disclosure
- Data loss due to intentional theft by employees, third-parties like contractors, or external actors
Hybrid work and Bring Your Own Device (BYOD) have increased these risks, and make it easier for employees and contractors to circumvent your existing data loss prevention technologies.
Digital workplace governance capabilities
Seraphic Security provides a comprehensive set of tools for preventing corporate data loss and data leakage via bowsers as well as widely used collaboration tools like Asana, Microsoft Teams, Notion, and Slack that make up the digital workplace.
Seraphic’s DLP engine is a proxy-less solution that performs all scanning locally so no data is transmitted or stored outside the organization. Capabilities include:
- Detecting and blocking encrypted file content
- Scanning and determining whether to allow or block password-protected compressed archives (e.g., .zip, .rar, .7z files)
- Using Optical Character Recognition (OCR) to inspect non-text files for sensitive data
Organizations can define and identify sensitive data using a combination of:
- Pre-defined patterns
- Personally Identifiable Information (PII) such as names, addresses, dates of birth, international phone numbers, passport numbers, national ID numbers, Social Security Numbers, etc.
- Financial information such as routing numbers, credit card numbers, International Bank Account Numbers (IBAN), SWIFT codes, etc.
- Medical record details such as doctors’ names, patients’ names, or medical record ID numbers
- Cryptographic material such as PGP private key blocks, RSA private keys, and SSH private keys
- API keys
- Account information such as Basic Auth username/ password combinations or OAuth tokens
- IPv4 and IPv6 IP addresses
- Custom regular expressions (regex)
Data loss prevention rules include:
- Enabling and disabling user actions in the browser, including copy/ paste, print, screen capture, right click, and view page source
- Restricting file upload by size and extension
- Redacting / masking in web pages and downloaded files
- Watermarking internal and SaaS web app pages
- Controlling data sharing between sites/ apps based on data source and destination
Seraphic Security’s fine-grained controls provide effective data leakage prevention across browsers and collaboration apps that constitute the digital workplace.
Data loss prevention policies can be configured to operate in Passive Mode (generate event only) or Active Mode (generate alert and take action). All events and alerts can be exported to log aggregation systems for analysis, audit, or investigation.
Using Seraphic Security for enterprise data leakage and loss prevention
Seraphic Security is for any organization that:
- Needs to protect enterprise data in browsers and desktop clients for SaaS services
- Needs consistent enforcement of their data loss prevention policies across a mix of employees and third-parties using both managed and unmanaged devices
- Needs an accurate audit log of who and when enterprise apps and data were accessed
- Wants to avoid the cost and complexity of proxies, Deep Packet Inspection (DPI), SSL interception, and API connectors
Existing enterprise data loss prevention products were designed to be deployed on-premises and control only email and endpoint storage. Seraphic Security extends an organization’s data leakage prevention strategy by filling the gaps left by legacy, proxy-based solutions.





