Digital transformation and digital workplace initiatives began gaining traction before hybrid work, but it wasn’t until hybrid work became widespread that the implications for data loss prevention became apparent. The vast majority of tools intended to stop enterprise data leakage focus on one of two channels: email or endpoint storage (including removable media). When both users and resources were centralized, these controls were generally effective since the primary objective was stopping data from leaving the premises.
The erosion of legacy DLP approaches
The decentralization of workforces and the increasing popularity of SaaS applications caused more data sprawl and gave rise to new channels (or vectors) for data loss. Because email as a method of sharing files and data was decreasing in popularity and local filesystems were becoming one of many places corporate data could exist, cracks began to show in existing DLP solutions. In an effort to protect data as it moved between endpoints and the cloud, vendors combined the data loss prevention capabilities that had been designed for email gateways with web proxies.
When either users or resources are centralized, proxies may be effective because a choke point exists that can be used prevent corporate data loss. However, they may be hindered by transport-layer encryption or require more compute resources to be able to perform in-line decryption, Deep Packet Inspection (DPI), and re-encryption. A mix of distributed users and distributed resources can create challenges for proxy-based data loss prevention, since it is much more difficult to ensure that all traffic is forwarded through the proxy.
Consider the following matrix:
| Centralized resources | Distributed resources | |
| Centralized users |
Data doesn’t leave the premises
|
Forward proxy in front of users enforces data loss prevention policies
|
| Distributed users |
Reverse proxy in front of resources enforces data loss prevention policies
|
Requires mix of forward and reverse proxies + complicated traffic steering
|
Unmanaged endpoints such as those used by third parties or that are part BYOD/ BYOPC initiatives also present a significant challenge for proxies, since it can be difficult or impossible to force traffic from those devices through a proxy (or it can be difficult to separate unrelated traffic).
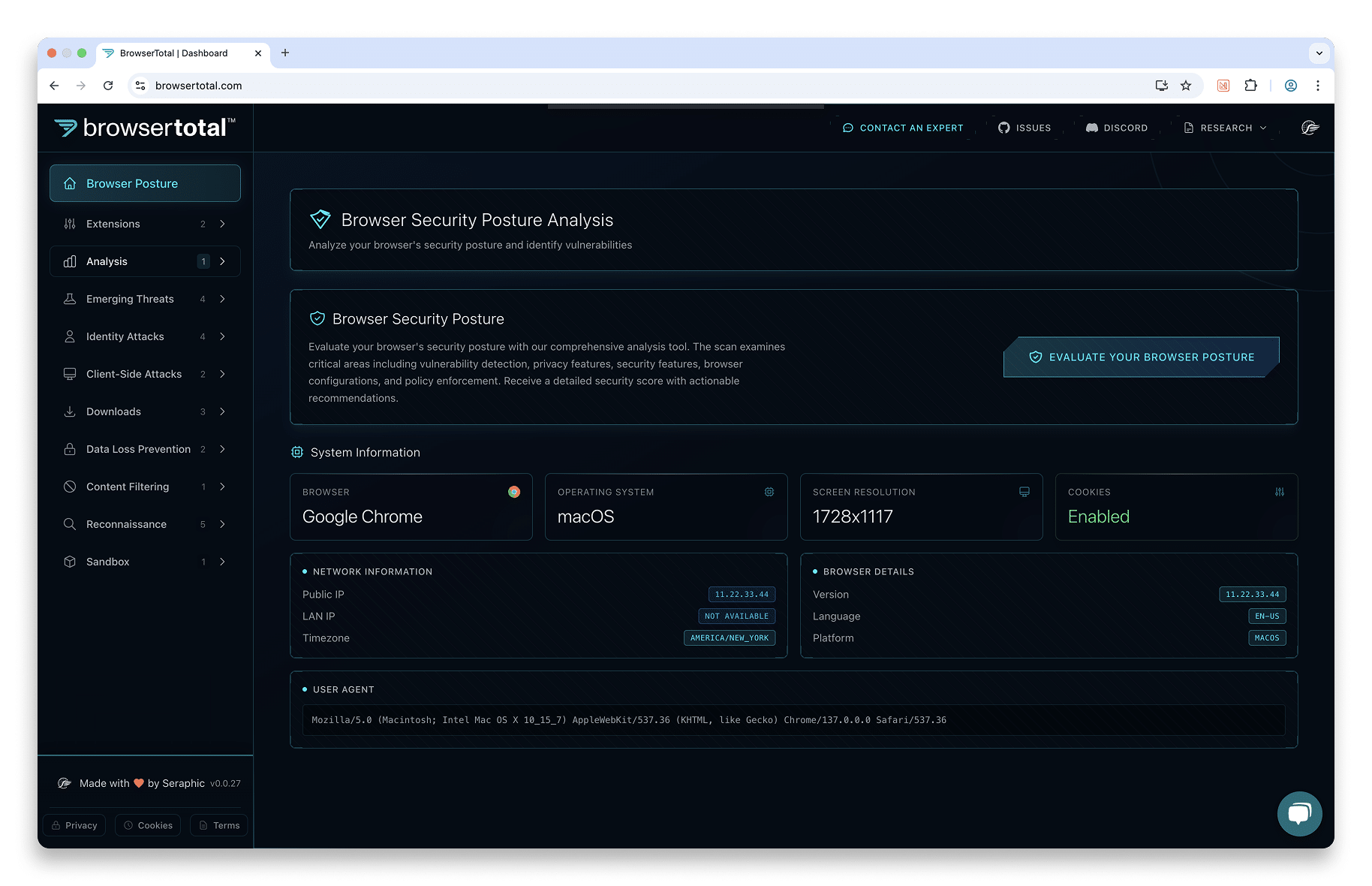
Modern data loss prevention techniques
With the cost and frequency of breaches rising, organizations must revisit their data loss prevention tools. Whether it is their access to internal and SaaS web apps or cloud storage, web browsers can be either a new and difficult channel to monitor and control or a vital tool for preventing corporate data leakage and loss. By embedding policy and governance controls in the browser—the place where data is handled—organizations significantly improve their visibility and better protect their data against accidental or intentional leakage and loss without the issues that plague proxies. Seraphic Security offers a comprehensive set of controls for user actions in the browser, as well as controlling the flow of data between sites. For more information about how Seraphic can help protect corporate data from leakage or loss, visit our Data Leakage and Loss Prevention use-case page or contact us to schedule a demo.