ChromeOS and Chromebooks have been wildly successful in sectors like K–12 Education because of their simplicity and ease of use. They also enjoy a reputation for being safer and more secure than conventional endpoints. That reputation stems from the fact that, under the hood, ChromeOS is heavily customized and hardened version of Gentoo Linux which treats the Chrome browser as the main user interface and an operating system in its own right: virtually all the applications that ChromeOS supports must run in the browser (while it’s true that ChromeOS can also run Android applications, they either rely on WebView—meaning that they still have a browser dependency—or have a user experience that is vastly inferior that offered by their native platform making them unpleasant or impractical to use). This approach would seem to limit the overall attack surface and leads to the question “do I need EPP and/or EDR on ChromeOS/ Chromebooks?” As is often the case, the answer is more nuanced than it might first appear.
Built-in security features of ChromeOS
Chromebooks incorporate a number of modern security measures, including read-only filesystems, verified boot, automatic updates, browser sandboxing, data encryption, and a recovery mode. ChromeOS also benefits from security capabilities that are part of the Chrome browser such as Safe Browsing.
Unfortunately, some of these measures are reactive in nature:
- Automatic updates are useful, but only if and when a vulnerability has already been identified and patched. Such updates can shorten the patch gap, but they don’t eliminate it and they don’t prevent zero-day exploits.
- Verified boot offers protection only if the compromised component is part of the boot process.
- Safe Browsing (as it exists in Chrome) only filters well-known malicious sites and malware (i.e., it uses threat intelligence and signatures to build a deny list) and won’t protect against sophisticated phishing attacks, web-based attacks.
Others, like browser sandboxing and data encryption, may help to contain certain types of attacks but don’t protect against others. It’s logical, therefore, to consider EPP and EDR for ChromeOS and Chromebooks to bolster the built-in security capabilities just as they do for traditional endpoints.
Using EPP and EDR for ChromeOS
Staples of endpoint security like EPP and EDR have limited effectiveness on ChromeOS. In most cases, they simply cannot be installed. Even, if they can be installed, the telemetry that can be collected to identify threats and the actions that can be taken to mitigate them are severely limited. EPP and EDR usually hook the OS kernel to monitor system calls and other events, but that isn’t possible on ChromeOS. More importantly, the Chrome browser has a self-contained execution environment composed of “helpers” (e.g., the DOM renderer, the JavaScript Engine, etc.) that are completely opaque to EPP and EDR. Since the bulk of both the user activity and potentially malicious activity occurs within the browser process or its children, EPP and EDR are unable to monitor or intervene.
The real challenge
Even if all of these measures were effective, they are primarily designed to prevent compromise of the underlying OS but—unlike conventional endpoints running macOS or Windows—ChromeOS is a much less interesting target insofar as very little valuable information is stored locally. Moreover, OS compromise is not the only concern. Capabilities such as anti-phishing, DLP enforcement, content filtering, and audit logging require additional tools (all of which must be deployed outside the endpoint).
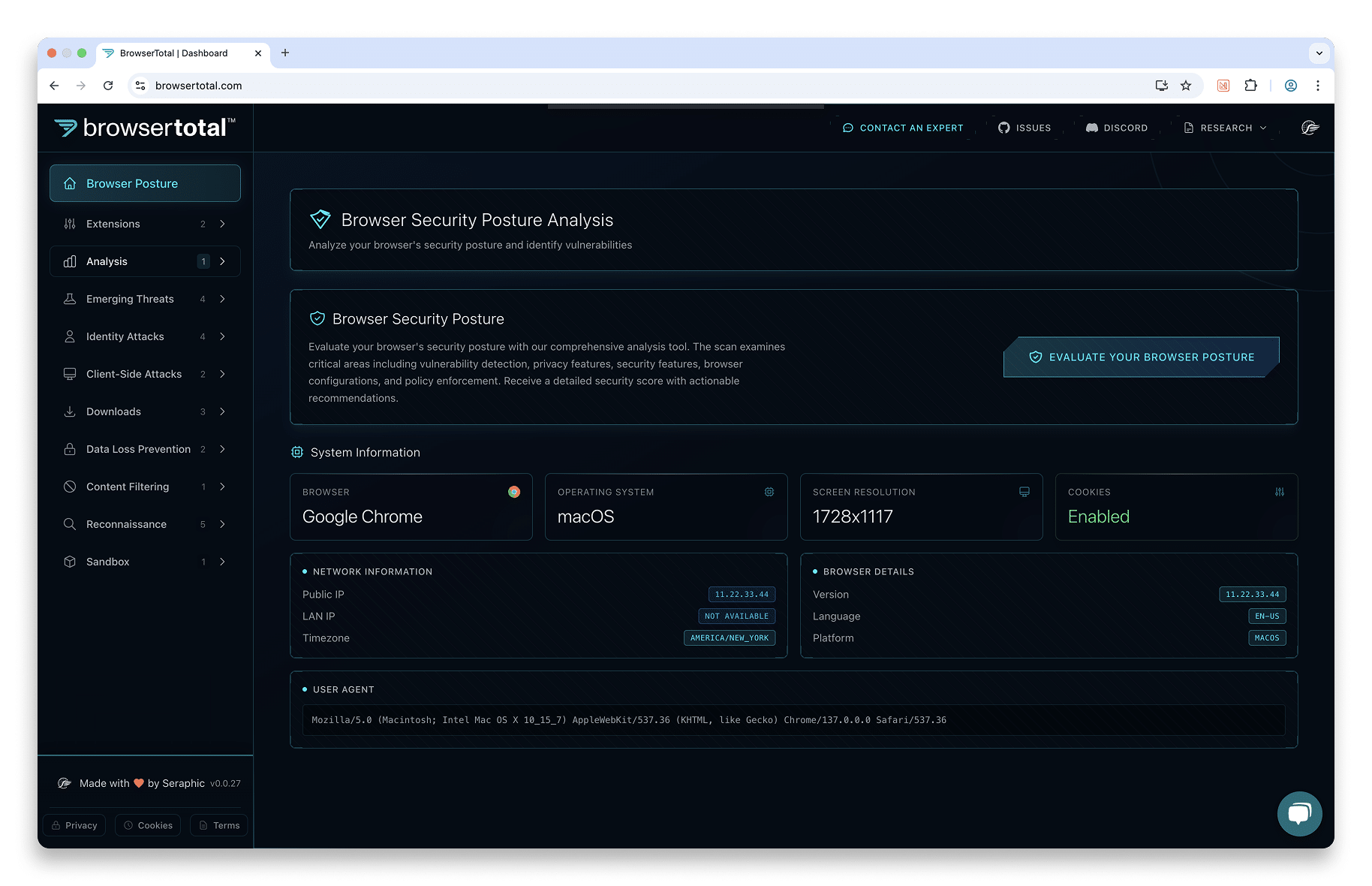
Seraphic Security’s enterprise browser security agent operates directly in the browser, enabling it to deliver unique security capabilities to Chromebooks, creating the first enterprise-grade security solution for this unique class of endpoints. For more information on how Seraphic can protect Chromebooks, visit our Use-cases page, download our solution brief, or schedule a demo. For more information on Seraphic’s real-world performance, download the ESG Technical Validation.